As you may have heard by now, the Department of Defense (DoD) rolled out an updated CMMC model yesterday afternoon – CMMC 2.0. Without further adieu, let’s get into the details…
What You Need to Know
This updated model is currently under public review and until it is accepted, all CMMC requirements are on hold. CMMC should not be included in any contracts or provisional assessments until the rulemaking process of CMMC 2.0 is completed. The timeline of this process will take anywhere form 9 to 24 months.
New Structure
The main change to be aware of is the overall structure of CMMC. In CMMC 1.0, there were five different levels; Level 1 was the most basic and Level 5 was the most advanced. In CMMC 2.0, the levels have been condensed into only three instead of five (Level 2 and 4 have been eliminated). To summarize:
- Level 2 of CMMC 2.0 is the old Level 3
- Level 3 of CMMC 2.0 is the old Level 5
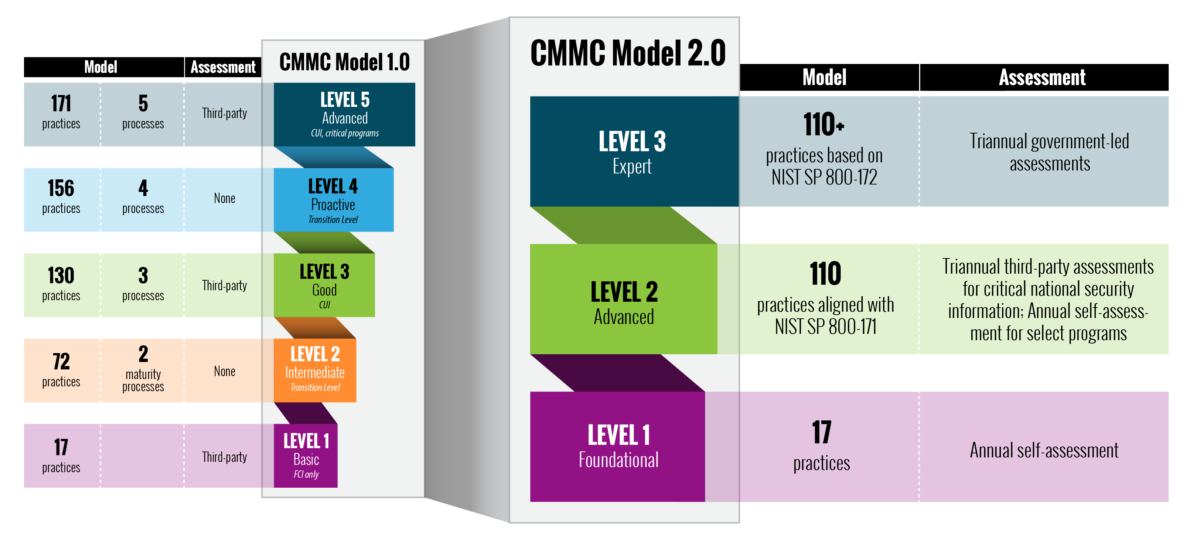
Some of the levels’ practices (ex: Level 3) are still under development and maturity controls were removed. However, you should expect to still recognize a lot of requirements from the old version. One of the primary changes you will notice is in Level 1. Previously, all formal assessments across all levels were required to be done by a third party. However, in CMMC 2.0, Level 1 now permits organizations to do a self assessment.
Other Items to Note
- POA&Ms will now be permitted in specific cases as long as there is an enforceable timeline (Some items will not be allowed to be on a POA&M)
- The ability to have a POA&M will require a minimum score report
- The DoD will determine the required CMMC level for a contract
- Assessment guides, assessor guides, domains, and controls will be solidified in the coming weeks but are expected to be rooted in the NIST SP 800-171 framework (just as before)
Why CMMC 2.0?
Based on a significant number of public comments in response to CMMC 1.0, it has become apparent that the following changes were necessary:
- More affordable (especially for small businesses)
- Increase trust in the CMMC assessment
- Clarify and align cybersecurity requirements with other federal requirements and widely accepted standards
All in all, these changes are being made in order to better improve the cybersecurity of the defense industrial base.
What You Need To Do
This is all very new information and you may be wondering, “What should I do in the mean time?” Bravo’s recommendation, is to focus on using security best-practices (DFARS and NIST SP 800-171) to improve your overall cybersecurity posture.