Protecting your organization’s data should be your #1 priority. However, with the transformation to the cloud and increasing reliance on remote work, this task has become more and more complex. More places to protect means more doors are opened for malicious attempts to infiltrate an organization; and traditional security practices no longer provide sufficient protection. It is for this reason that the adoption of the Zero Trust mindset and framework is on the rise. By taking a deep dive into the core of what Zero Trust is, we’ll see why it’s crucial for an organization. On top of this, we’ll also examine why Zero Trust cannot be successfully implemented without considering the people side of business.
What is Zero Trust
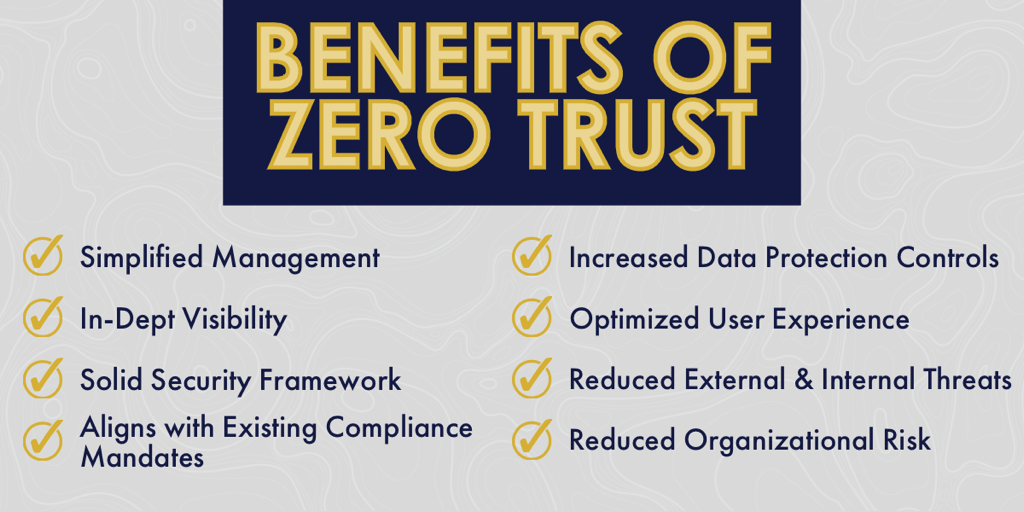
In short, Zero Trust is a security framework that requires all users to be authenticated and authorized before being granted access to each application and data. Although Zero Trust is a simple concept, application is not as simple. It is the proposed answer to how an organization keeps their environment secure, while maintaining collaboration and productivity and staying compliant with NIST 800-207. Zero Trust targets a “perimeter-less” environment with the ultimate goal being that any asset that is compromised has minimal to no impact on any other asset. In other words, using Zero Trust means that if any one system or user is compromised, the breach doesn’t compromise the rest of your systems because it is self-contained and controlled. This helps you to save tons of money in the event of a breach due to Zero Trust’s ability to keep the breach contained, giving you a single place to concentrate your investigation and repair.
According to the Cybersecurity & Infrastructure Security Agency (CISA), there are five core pillars that are critical to the successful implementation of Zero Trust: identity, devices, networks, applications, and data. While these are all important, there is one that seems to be missing – workspaces. According to our partners at AvePoint, “Ignoring collaboration environments like Microsoft Teams or Groups when building your data protection strategy is a dangerous pitfall to your security. These spaces are hubs of collaboration and information sharing for most organizations yet controlling who has access to what is not always top of mind, Left unchecked, you could end up with overprivileged users, unsecured collaboration spaces, and an exponential increase in risk.” To put it another way, this “Sixth Pillar” is where day-to-day productivity really happens, and we often take it for granted. To learn more about Zero Trust’s “Sixth Pillar”, check out AvePoint’s blog here.
The Shift from Traditional Security
Zero Trust is a major shift from previous security models. In the old model, there was an assumed amount of trust on certain network segments. For example, if a user was logged in or an app or system was active behind the firewall, then they were trusted, meaning a person, once behind the firewall can go anywhere and do anything. In contrast, the motto behind Zero Trust is “Never Trust and Always Verify,” hence the name Zero Trust. At its core, it means that every person, must reverify (not necessarily re-login… Single sign-on helps) that they should and do have access to each system or application. This is the concept of “Micro-Segmentation;” each application, or system is its own little world, and a person logging in who doesn’t have a reason to is blocked. After all, why should your technologist be able to see your financials? Micro-segmentation dictates that only your finance team and the Finance administrator has access to that! When each system is treated this way, it means that unlike today, one person (or one account grabbed by a hacker) cannot access everything behind the firewall.
This truly only works when you marry the concept of micro-segmentation to real time monitoring (a look at everything that is going, all the time). For example, systems like an advanced SIEM (Security information and event management) or an EDR (EndPoint Detection and Response) can continuously survey the entirety of the organization’s digital assets and gives a bird’s eye view of every packet and connection within your organization. Additionally, implementing Zero Trust with these kinds of advanced technologies enable real-time monitoring to keep data and users secure, flexible, and operational. It is a complete security solution. However, we cannot forget about the Sixth Pillar… Collaboration systems like Teams and M365 need to be openly accessible and closely monitored in order to avoid impacting productivity while also maintaining strong security. So, how does this all come together? Luckily, Bravo has your back! Our cybersecurity experts can help your organization implement the technical controls needed to achieve a strong Zero Trust framework. To learn more about Zero Trust and how we can help, check out our whitepaper.
The People Side of Things
This brings us to the next most crucial step in completely securing your organization – the people. If an organization’s security and people are misaligned, you cannot achieve the full results of Zero Trust. In a study done by CA Technologies titled, Why IT Needs to Lead Now: The Innovation Imperative, the results suggest that the reason many opportunities are missed is due to the disconnect between IT and business. CA Technologies surveyed 800 global businesses and IT executives and found that 34 of the respondents characterized their relationship with IT as “combative, distrustful, or siloed.” 31% of IT executives surveyed agreed with this assessment.
If there is not a trusting, collaborative relationship between IT and business, not only will the organization’s success be impacted, but so will the security of the organization’s data. IT can implement as many security practices as they’d like, but if they fail to consider their employees day-to-day and gain their overall support, a business can never be truly secure. This is often due to security teams having a certain objective that they expect the business side to align with without having much of a say. While there is no malicious intent behind these actions, it can still really impact the overall company culture.
How to Bridge the Gap
Bridging the gap between people and security can be a daunting task without the right shepherds, as both sides are seeking to complete their job to the best of their ability. However, there are several practices an organization can implement to find harmony between IT and their other employees. The first and perhaps most important strategy is COMMUNICATION! Having an open dialogue is key to bridging this gap and keeping everyone involved. IT should communicate and plan with their peers. As IT language can become confusing for those that are unfamiliar, it is critical to find a common ground so that communication is still able to come from both sides. Afterall, if you want to control and micro-segment a system, the first people who can tell you who really ought to have access are the business users that own that system; your Finance and Accounts Receivable Team for your Finance / ERP system and so on! While security needs to ensure business continuity and user-safety, it should work to align with business objectives as well. Ensure this is done in an open environment (rather than remotely over email), incorporating users as stakeholders, conversationalists, and active participants. Doing so will allow the discussion to flow and help everyone build a winning and secure environment together!
As previously discussed, trust is crucial. From the business perspective, they should not have to question whether IT will deliver on their promises and vice versa. In order to eliminate distrust, the focus needs to be on understanding how the business user’s culture works within your specific organization. Additionally, it’s necessary to consider how an IT initiative will impact the day-to-day business. One of the ways companies can seamlessly implement Zero Trust is through multi-factor authentication. An example of this would be Microsoft’s Window’s Hello combined with Active Directory. This not only helps maintain security, but also makes Zero Trust easy on the employees because it provides a single way to login and use Windows and cloud applications. This brings us back to Adoption & Change Management (ACM)… Including and educating all stakeholders is essential to success, especially if you want a business user to recognize when someone has access to something they shouldn’t. Through our ACM services, Bravo helps organizations learn and adapt to new technology and methodology initiatives, ensuring an adaptive and learning culture. Not only can our trainers help educate and prepare your employees for change, but we also help establish a common ground for managing the impact of change and technology across the organization.
How Bravo Can Help
There is a lot to think about when it comes to Zero Trust, and it is often the detail that matters when preparing your organization for next-generation security. Let Bravo & AvePoint do the thinking and heavy-lifting for you. Bravo has 12+ years of proven experience delivering AvePoint solutions to federal agencies to help strengthen their security posture and achieve compliance. By pairing AvePoint’s Zero Trust Solution with our implementation and Adoption & Change Management services, you will benefit from the ultimate recipe for success by achieving the right balance between security and collaboration.
Considering taking the leap to Zero Trust? Our security experts can help streamline your Journey. Fill out the form below to get in contact with one of our experts!